Each Cisco phone uses an ITL (Initial Trust List) and additionally, if security is enabled, a CTL (Certificate Trust List) that store a list of server certificates in the phone flash.
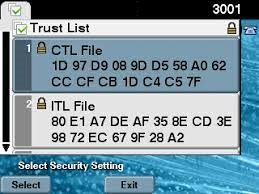 CTL and ITL signatures shown on Cisco phone in Security menu. The signature is the MD5 or SHA1 hash of the file. |
The mismatch between the CTL or ITL files installed on a phone and the CUCM (Cisco Unified Communications Manager) cluster can cause the following serious issues:
|
To detect ITL/CTL signature mismatches you can generate the following reports with UPLINX Phone Control Tool:
-
- ITL report with the ITL report wizard.
- CTL report with the CTL report wizard.
The reports are generated in HTML and CSV format and allow you to easily detect Cisco phones that have a mismatched (wrong) ITL and CTL. With the UPLINX Bulk Erase wizard, you can then clear the configuration from remote if the phone can still be controlled.
View sample CTL signature mismatch report in HTML.
To generate the CTL or ITL signature reports, it is required that the web page of Cisco phones is reachable, and the phones must be registered with CUCM.
Read more about 'Why does a Cisco phone not apply new config settings?'
The UPLINX Phone Control Tool's ITL or CTL Report wizard helps you find phones with wrong ITL or CTL signatures without visiting each phone - though phones must be registered.
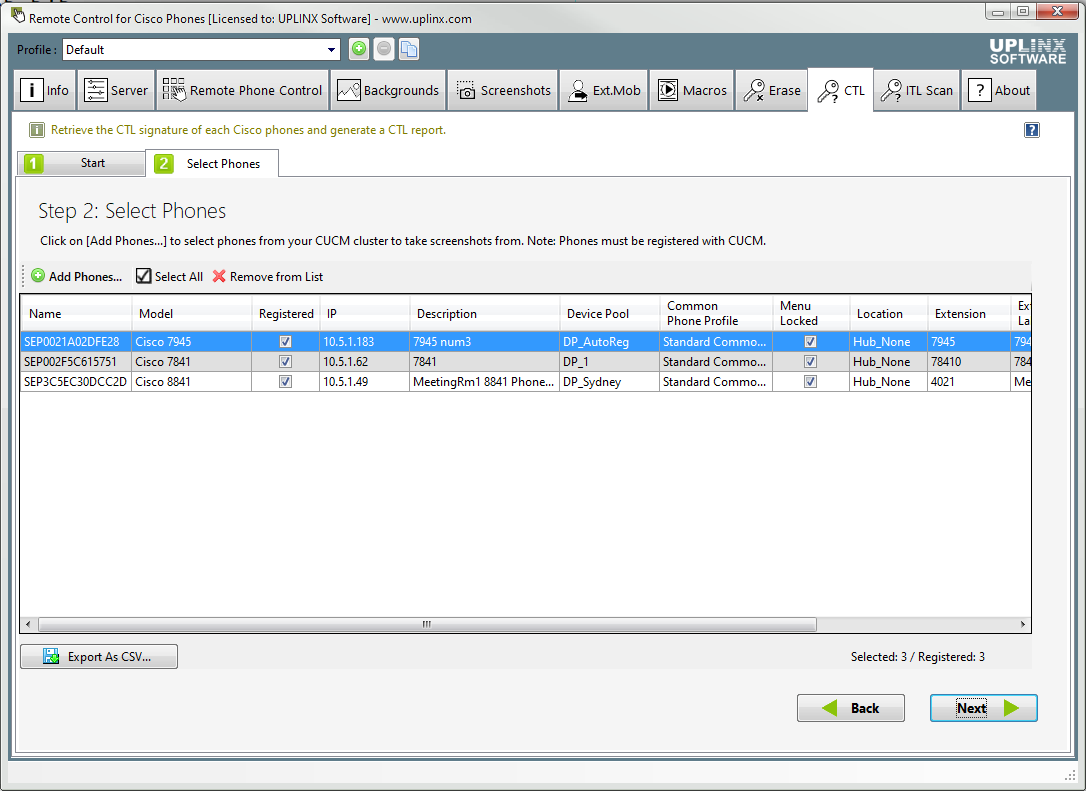
CTL report wizard to find mismatched CTL signatures on Cisco phones
The UPLINX Phone Control Tool helps you to find incorrect CTL or ITL signatures and can erase all security settings on Cisco phones from remote:
- Identify invalid CTL or ITL files: Use the free ITL report or the CTL report wizard.
- Erase ITL or erase all security settings from Cisco phones: Use the CTL/ITL Erase wizard.
- Migrate phones to a new CUCM cluster: Easily select a single or group of phones to migrate to a new CUCM cluster by deleting CTL/ITL files. The phones can first be chosen based on device pool, model, extension range, location, or phone description. Please see the steps 'How to migrate Cisco phones to new CUCM servers'.



