Track & Audit - Configuration Change Tracking for Cisco Unified Communications
UPLINX Track & Audit is an enterprise grade, web-based configuration tracking and change management audit system for Cisco Unified Communications that automatically tracks configuration changes to enable version and revision control. With multiple administrators making modifications, Track & Audit lets you review the what, when and who of any modification. Track change events, receive alerts by email, view the original and new value to roll-back to the previous settings when problems occur.
Configuration Change History
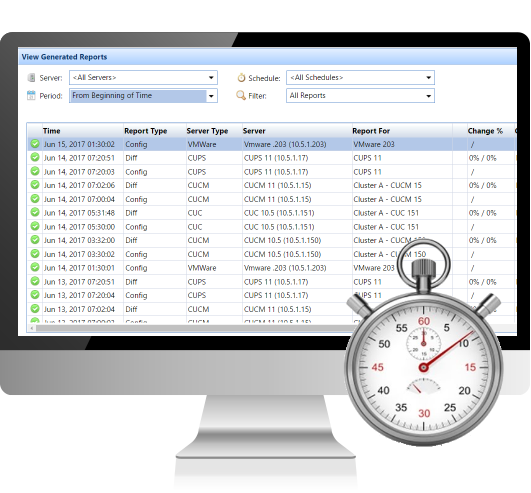
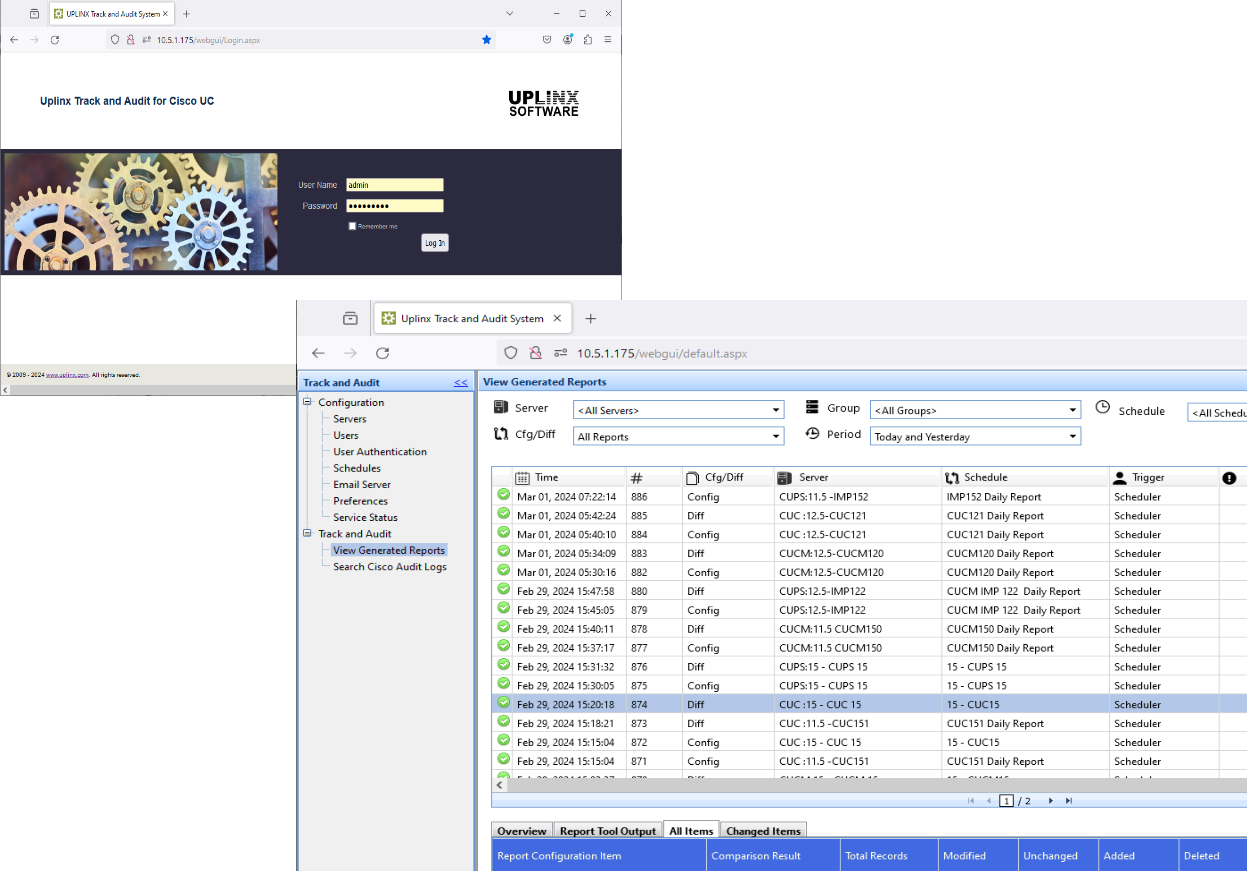
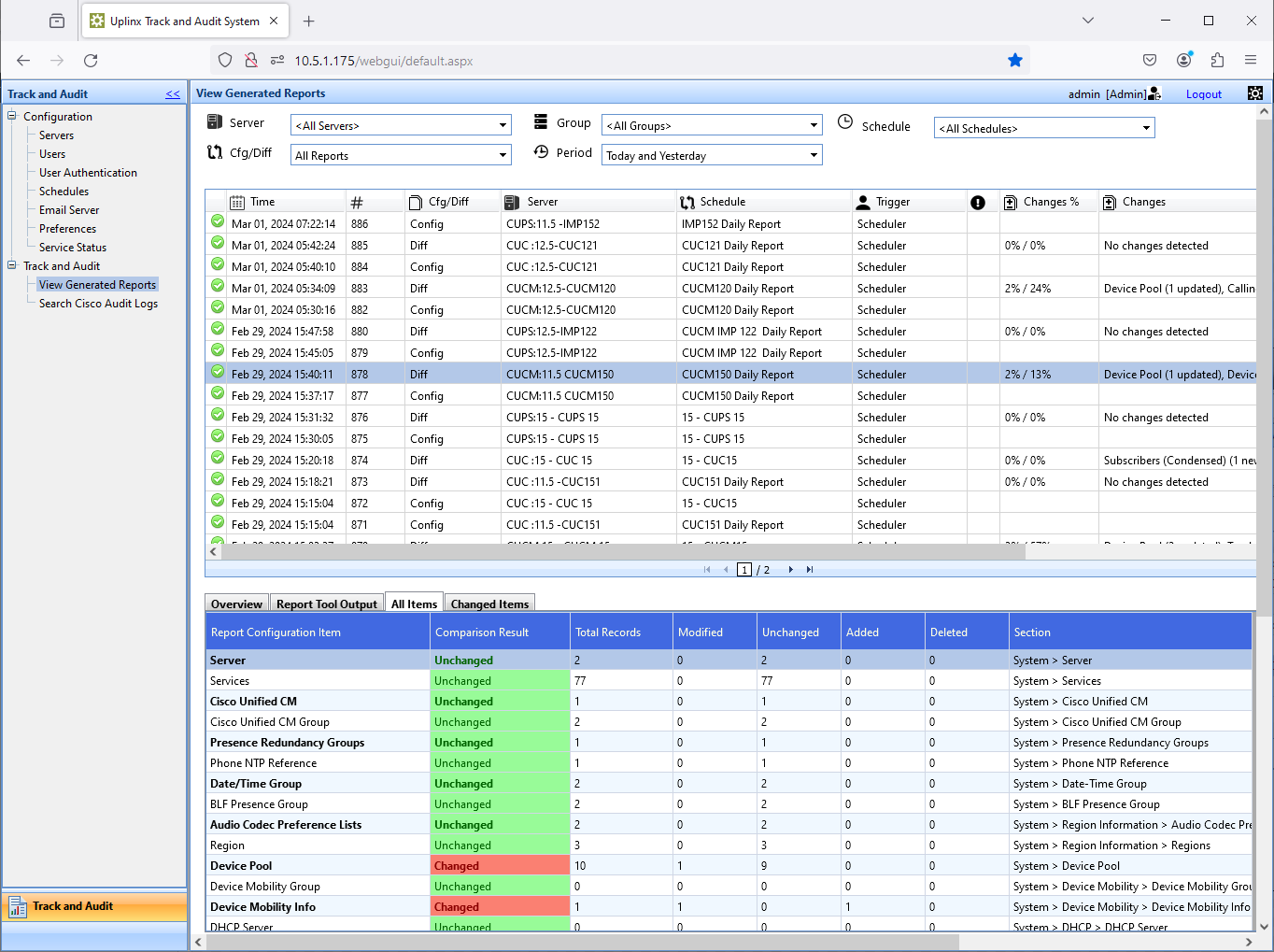
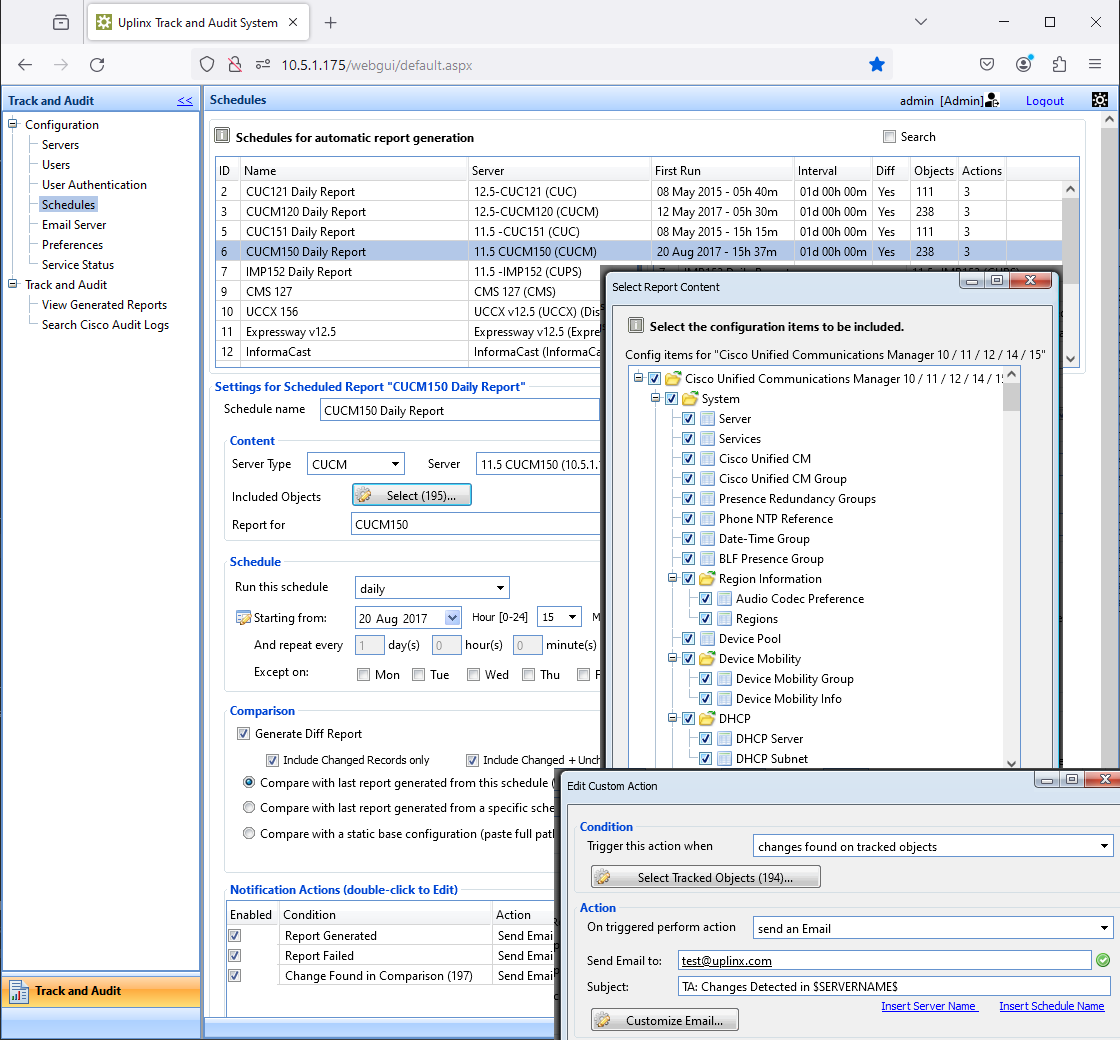
Using a scheduler, Track & Audit generates configuration reports and comparison diff reports for all Cisco Unified Communications servers and stores them to a report repository. Reports can contain every configuration item of Cisco Voice with all settings. The Web interface allows you to easily define which configuration items are documented in the reports. Create specialized reports to track ongoing issues.
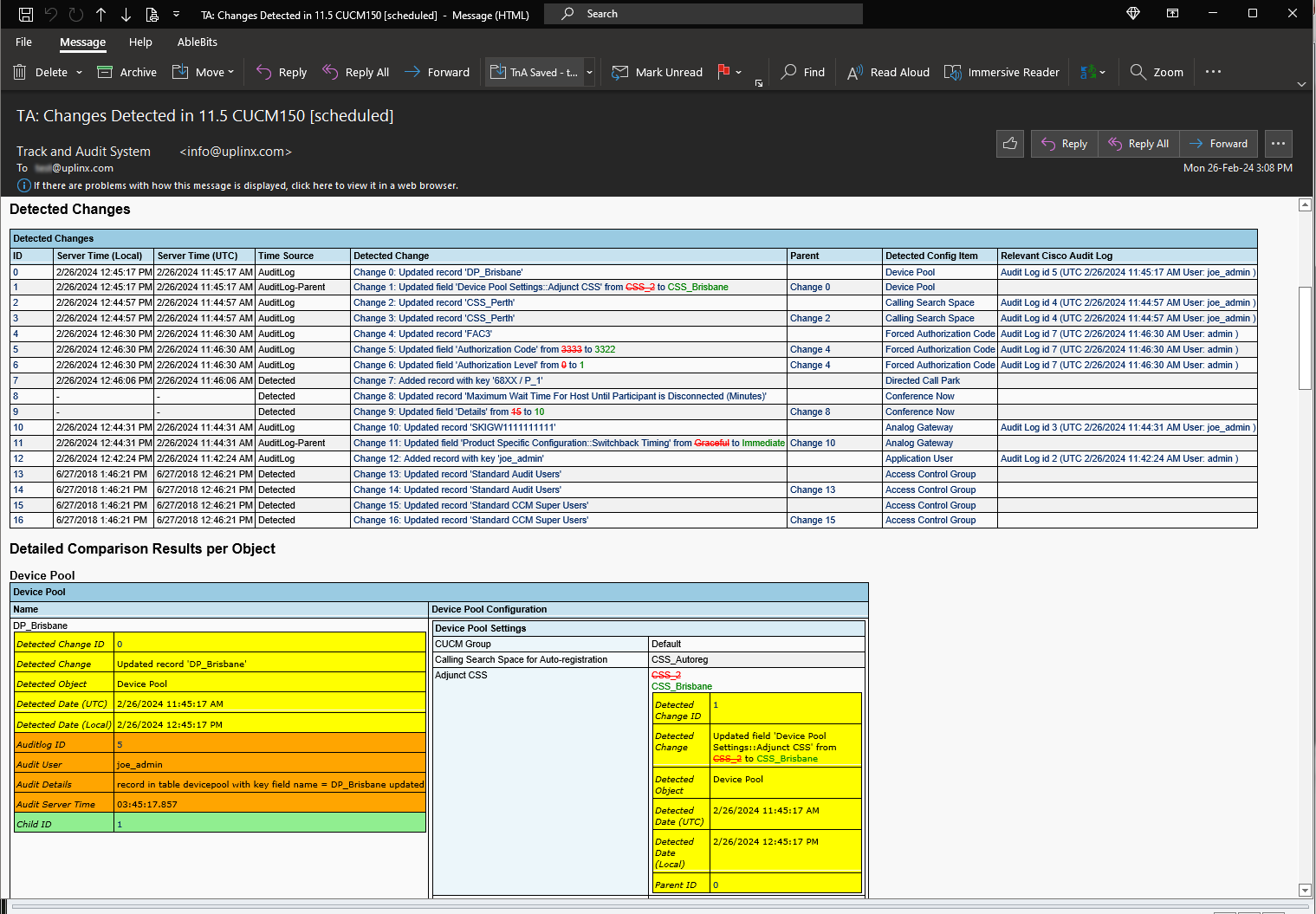
Track change events with email alerts
Critical configuration elements to be monitored can easily be defined on the web interface. Any CUCM, IMP or CUC configuration item such as device pools, CSS, route patterns, users, translations, and other system-relevant items such as trunks or voice gateways, can be automatically monitored and trigger email notifications to an administrator if they are changed.
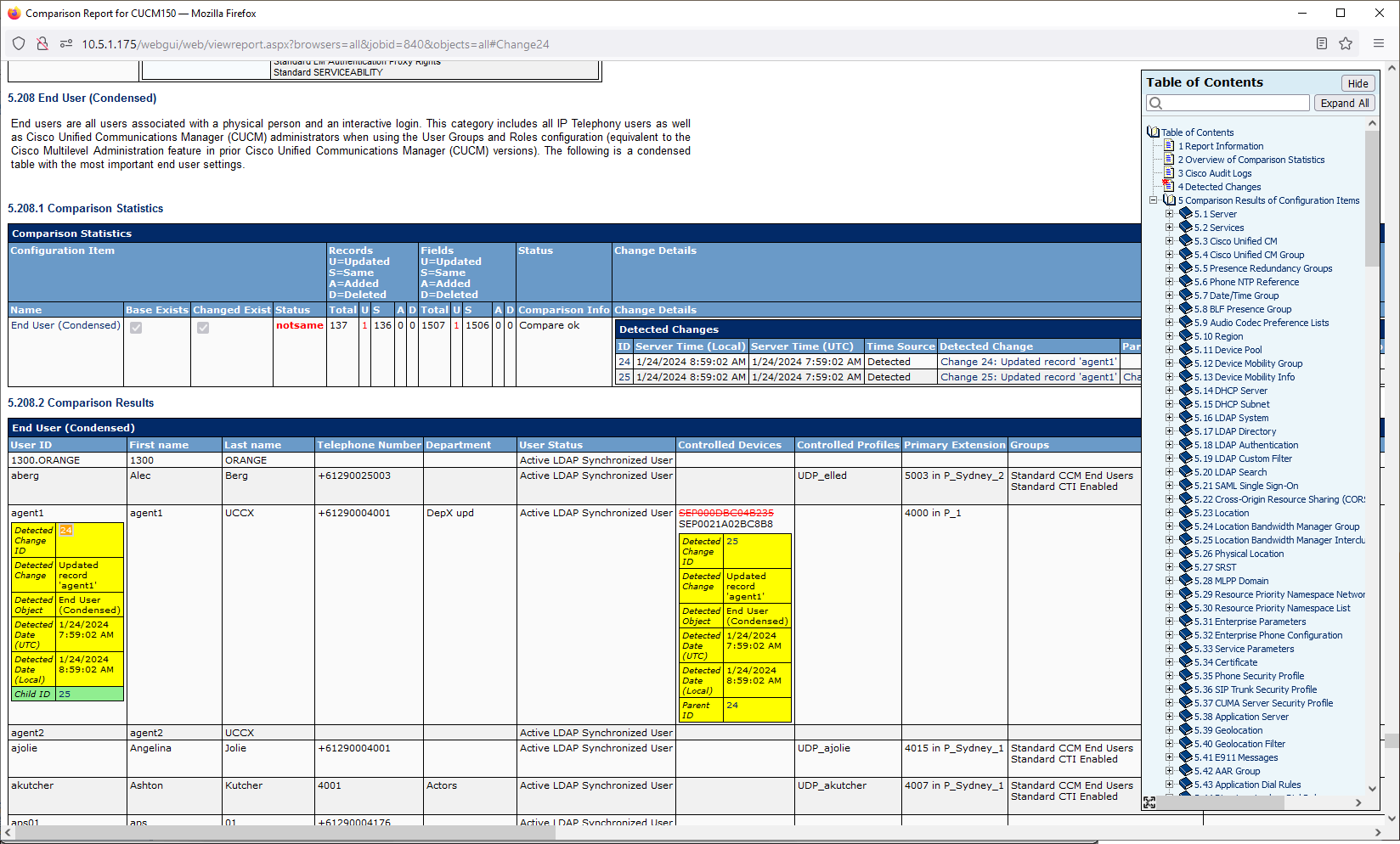
With UPLINX Track & Audit, you can easily generate configuration and comparison reports that contain detailed data on configuration changes to Cisco Unified Communications – see who, what and when. These audit reports and email alerts contain audit data to easily track, log and review any changes. They tell you what the old value was and what it has been changed to.
- Automatically backup configurations for all Cisco Unified Comms servers.
- Recover from accidental deletions and restore prior configurations.
- Identify how much work has been done, when and by whom.
- Roll-back to previous versions in case of system failure or user issues.
- Email alert administrators of changes to critical components. Easily define monitored configuration items.
- Rapidly review any changes made including userid, date and before and after values.
Configuration reports that contain Who, What and When?
UPLINX Track & Audit creates audit reports that show configuration changes - who, what and when - in Cisco Unified Communications. Cisco Audit Logs can be automatically merged for increased depth and accuracy of changes found and to provide evidence of who made the configuration change and when it was made.
Scheduled Configuration Backups and Repository
UPLINX Track & Audit automatically generates and stores configuration reports for backup purposes in its report repository. You access it by web browser, via user authentication with access controls, to view generated reports by server or date.
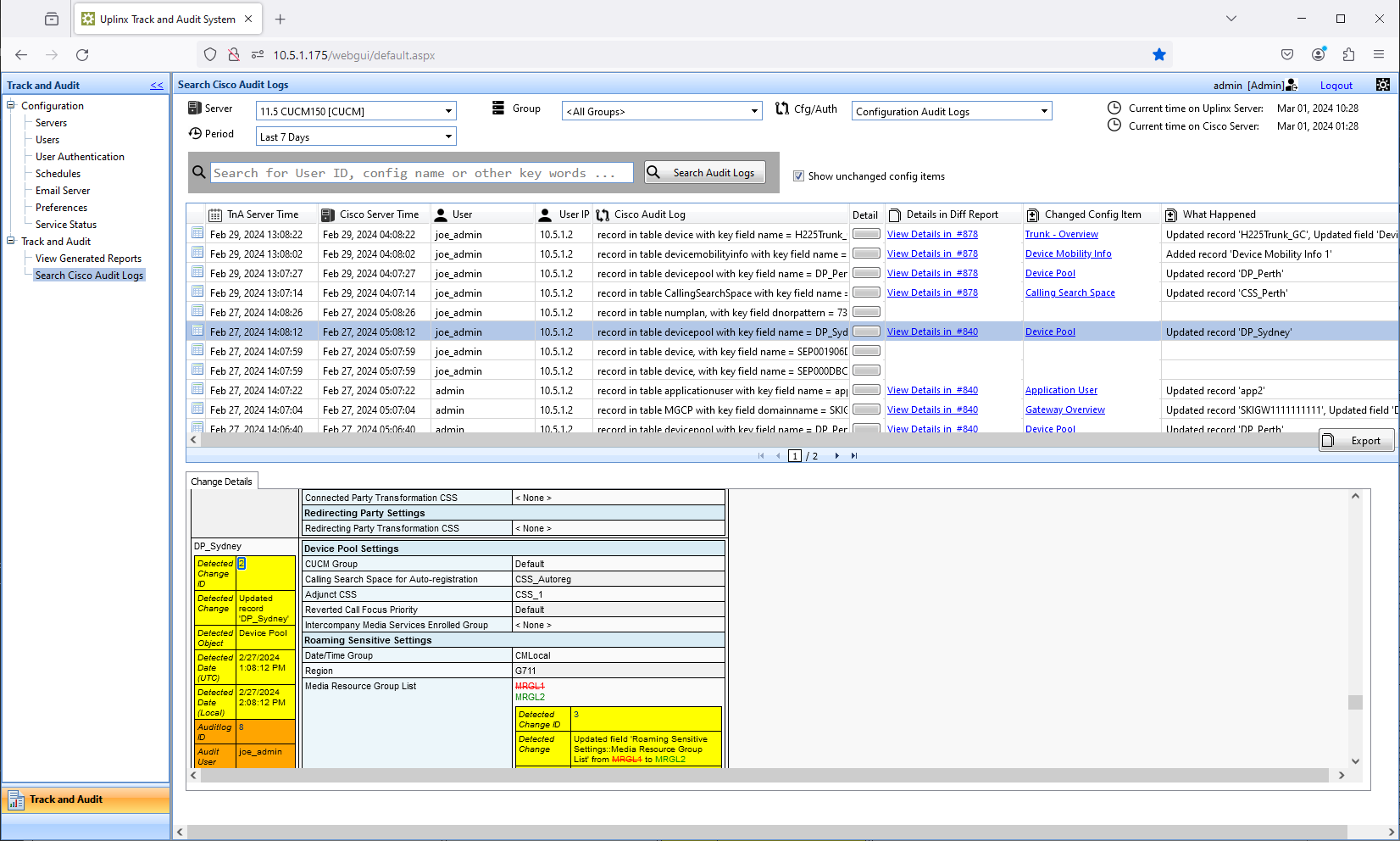
Simplify your review process by searching for changes in reports and Cisco Audit logs, or specify a search for critical configuration changes.
Receive email alerts when backups have been completed or only when critical configuration changes have been made.
Change Reports
Audit reports show the time of change events, the before and after values, and who made the changes to the Cisco CUCM, CUC or IMP configurations. Configuration reports and change or diff audit reports are automatically generated to identify any change made.
Audit reports can be accessed via the Track & Audit Console by any web browser. Access can be controlled per user and limited to specific servers.
Email Alerts When Critical Configurations Change
Define triggers to monitor and track important system configurations such as route patterns or voice gateways to alert administrators by email.
Cisco Audit Logs - Collection and Analysis
Search in Cisco Audit logs and identify all affected configurations from the Audit Log Console.
View and search for user login and logout activities and receive email alerts.
Restore to Last Known Good Configuration
Identify faulty changes quickly and then manually revert configurations to the last known good state. Configuration reports and audit logs are automatically generated and stored.
Web-Based, Enterprise-Grade System
- Self-sufficient, unique configuration management system for Cisco Unified Comms designed with security.
- Centralized, web-based solution running on Windows Server.
- Designed to operate multiple clusters in large and distributed environments.
- Multi-cluster, multi-user web based access with user access control.
- Cisco Server access only from Track & Audit server with firewalled security.
- Authentication of user logins via Active Directory means no dedicated passwords and no Cisco admin server access.

Take a look inside UPLINX Track & Audit. Keep track of changes to configurations on your Cisco Unified Communications servers, for auditing, accountability, and peace of mind. Track & Audit alerts you on changes, directly to your inbox. Quickly identify what has changed and revert changes if something goes wrong.